
In the digital age, the security of systems and processes is paramount. Safeguarding our systems and processes from vulnerabilities isn't just smart—it's vital. Vulnerability management stands at the forefront of cybersecurity, acting as the guardian of our digital realms. This guide dives into the intricacies of vulnerability management, shedding light on its critical role in protecting systems and processes from potential threats. We'll explore how identifying, assessing, and mitigating vulnerabilities not only fortifies our defenses but also enhances the resilience of our technological infrastructure. Whether you're a seasoned IT professional or just beginning to navigate the complexities of cybersecurity, understanding the nuances of vulnerability management is key to maintaining the integrity and security of your digital assets.
Understanding Vulnerability Management
Vulnerability Management is a continuous process designed to identify, classify, remedy, and mitigate vulnerabilities within an organization's IT environment. Unlike a vulnerability assessment, which is a one-time or periodic evaluation of security weaknesses, vulnerability management is an ongoing practice that ensures proactive threat prevention. It's a crucial component of any cybersecurity strategy, Helping organizations stay ahead of threats by systematically fixing weaknesses before malicious actors can exploit them.
The significance of vulnerability management cannot be overstated in today's cybersecurity landscape. With the increasing complexity and volume of cyberattacks, coupled with the rapid pace of technological advancements, organizations face an ever-expanding attack surface. Effective vulnerability management not only protects information and assets but also complies with regulatory requirements, thereby safeguarding an organization's reputation and financial health.
Step by Step Process of Vulnerability Management
Inventory and Asset Management: The foundation of effective vulnerability management is a comprehensive understanding of all assets within an organization’s network. This includes hardware, software, and any devices connected to the network. Keeping an updated inventory helps in identifying which assets may be vulnerable to specific threats.
Why is this comprehensive inventory so vital? First, it enables organizations to identify which assets are critical to their operations and which may house sensitive data. Understanding the value and function of each asset helps in prioritizing security efforts. For instance, a server containing sensitive customer information is a higher priority than a printer in a public area of an office.
Moreover, an updated inventory assists in pinpointing which assets might be vulnerable to specific threats. This is crucial because vulnerabilities often vary widely across different types of assets. A vulnerability in a Windows operating system will not affect a device running Linux, but without a clear inventory, such distinctions may go unnoticed.
Vulnerability Scanning: Performing vulnerability scans is an essential aspect of an organization's cybersecurity defenses. These scans utilize automated tools to thoroughly check systems, applications, and networks for known vulnerabilities. This proactive measure is essential for identifying security weaknesses before attackers can take advantage of them. With the cyber threat landscape constantly evolving, regular and comprehensive scans are indispensable for keeping pace with new vulnerabilities as they emerge. These scans range from surface-level assessments to deep, authenticated examinations, ensuring a thorough evaluation of potential risks.
The significance of vulnerability scanning extends beyond mere detection; it involves prioritizing vulnerabilities to strategize remediation efforts effectively. This not only helps in fortifying security measures but also ensures compliance with various regulatory standards, reflecting an organization's commitment to maintaining a robust security posture. By integrating regular vulnerability scanning into their security protocol, organizations can significantly reduce their exposure to cyber threats, safeguarding their digital infrastructure and sensitive data against potential breaches.
Risk Assessment: This step involves evaluating each vulnerability for its potential impact on the organization and the likelihood that it will be exploited by adversaries. Such an evaluation is important because it allows organizations to differentiate between vulnerabilities that could cause significant damage from those that pose minimal risk. Factors like the sensitivity of the affected system, the complexity of a potential attack, and the current threat landscape play critical roles in this assessment. By meticulously analyzing these aspects, organizations can rank vulnerabilities, ensuring that the most severe are remediated first, thereby optimizing resource allocation and enhancing overall security posture.
Furthermore, risk assessment is not a one-time task but a dynamic process that adapts to new threats and changes within an organization's network environment. As new weaknesses are found and old ones are fixed or lessened, the danger changes, requiring regular reassessment. This continuous cycle of assessment and prioritization not only helps in maintaining a resilient defense against cyber threats but also supports compliance with regulatory requirements, showcasing a proactive approach to cybersecurity. Effective risk assessment, therefore, bridges the gap between vulnerability identification and remediation, guiding strategic decision-making in vulnerability management.
Remediation and Mitigation: Remediation and mitigation form the action-oriented phase of vulnerability management, where identified risks are systematically addressed. Remediation involves direct action to fix vulnerabilities, often through patching software, upgrading systems, or altering configurations to close security gaps. This step is crucial for eliminating potential entry points for cyber attackers and requires a coordinated effort across IT and security teams to implement solutions efficiently. For critical vulnerabilities, swift remediation is essential to prevent exploits that could lead to data breaches, system downtime, or other damaging outcomes. However, the remediation process must be carefully managed to ensure that fixes do not inadvertently disrupt system functionality or create new vulnerabilities.
When quick remediation is not feasible—due to the complexity of a fix, compatibility issues, or resource constraints—mitigation strategies become vital. Mitigation means putting temporary measures in place to lower the risk of being exploited without directly getting rid of the vulnerability. Examples include adding firewall rules, segmenting networks, or applying additional monitoring to sensitive systems. These measures can significantly lower the likelihood of an attack succeeding until a permanent fix can be applied. Both remediation and mitigation require ongoing communication within the organization and with external stakeholders to manage expectations and ensure that security measures do not hinder business operations. Together, these strategies ensure that vulnerabilities are not just identified but effectively neutralized, maintaining the integrity and security of the organization’s digital environment.
Compliance and Reporting: Compliance and reporting in vulnerability management extend beyond the immediate goal of securing systems; they are about aligning with broader industry regulations and standards. This aspect is crucial for organizations operating in sectors where regulatory compliance is not just best practice but a legal requirement. Effective vulnerability management systems thus incorporate comprehensive record-keeping mechanisms that detail every identified vulnerability, the steps taken to remediate or mitigate these issues, and the current compliance status. Such documentation is vital for demonstrating due diligence and adherence to standards like GDPR, HIPAA, or PCI DSS, which govern data protection and privacy. Maintaining these records ensures that organizations can provide evidence of their proactive efforts to secure data and systems, which is crucial during audits or in the aftermath of a security incident.
Moreover, the process of compliance and reporting fosters a culture of transparency and accountability within an organization. It enables stakeholders to understand the organization's security posture, the effectiveness of its vulnerability management program, and areas needing improvement. Regular reports and updates also facilitate informed decision-making by senior management, ensuring that cybersecurity remains a central component of the organizational strategy. In essence, effective compliance and reporting not only help in meeting regulatory requirements but also play a critical role in building trust with customers, partners, and regulatory bodies, affirming the organization's commitment to maintaining a secure and resilient digital environment.
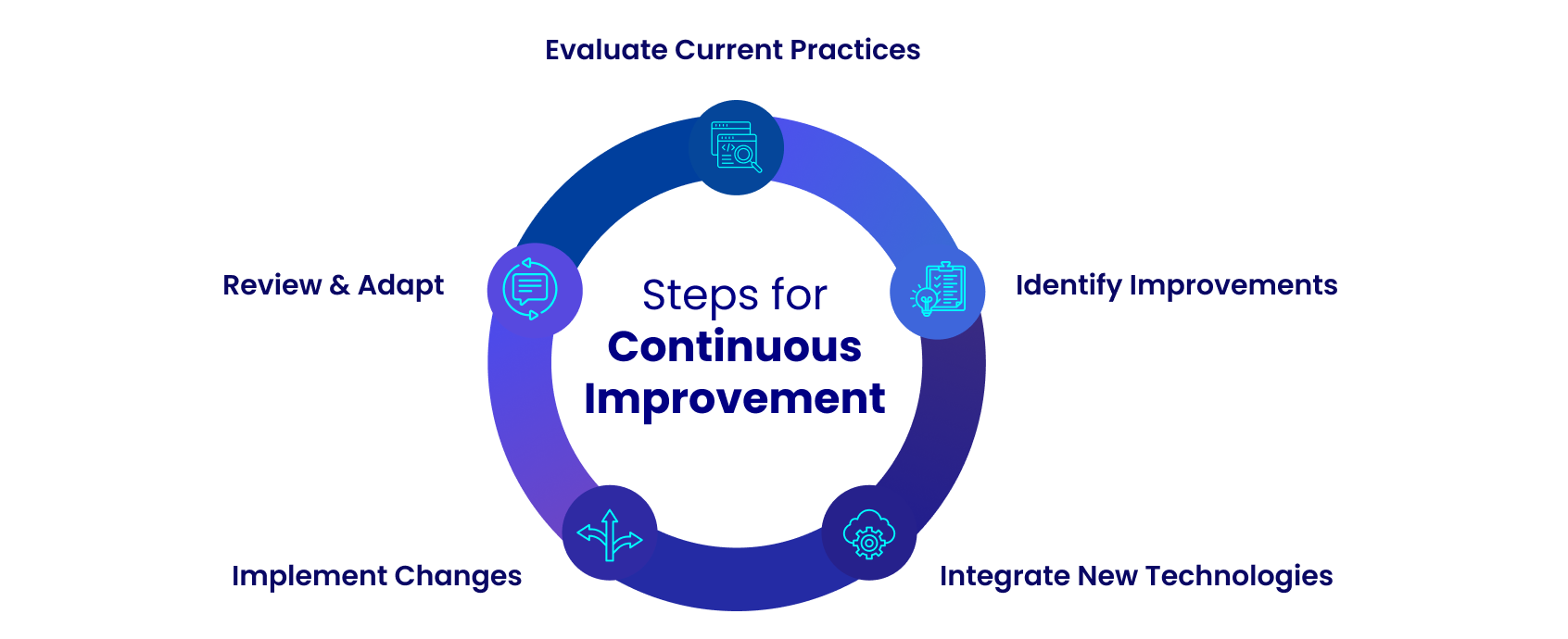
Continuous Improvement: Continuous improvement in vulnerability management is essential in an era where cyber threats evolve with relentless speed and sophistication. This dynamic landscape demands that organizations not just react to threats as they arise but also proactively refine and enhance their vulnerability management strategies over time. Regular reviews and updates of the vulnerability management process are critical to this effort, ensuring that practices not only stay effective but are also in step with the latest security standards and emerging threats. These periodic evaluations allow organizations to adapt to new technologies, incorporate lessons learned from recent incidents, and recalibrate their approach based on the changing nature of cyber risks.
Incorporating continuous improvement involves gathering and analyzing data on the effectiveness of current vulnerability management practices, identifying areas for enhancement, and integrating new tools and techniques that can better identify, assess, and mitigate vulnerabilities. It also means being aware of the latest cybersecurity research, threat intelligence, and best practices within the industry. Engaging in communities of practice, attending professional cybersecurity conferences, and participating in relevant training can provide valuable insights and knowledge.
Moreover, continuous improvement is about fostering a culture of security within the organization, where feedback from all stakeholders is valued and security practices are integrated into the fabric of daily operations. By making vulnerability management an ongoing process of learning and adaptation, organizations can build a more resilient defense against cyber threats, ensuring they are prepared to meet the challenges of tomorrow’s cybersecurity landscape.
Best Practices for Effective Vulnerability Management
Implementing a successful vulnerability management program requires adherence to several best practices:
Regular and Comprehensive Vulnerability Assessments: Conducting frequent vulnerability scans ensures that new and existing vulnerabilities are promptly identified. These assessments should cover the entire IT ecosystem, including on-premises and cloud environments. By thoroughly examining the entire ecosystem, including networks, applications, and systems, organizations can gain a comprehensive understanding of their security posture and prioritize remediation efforts effectively.
Prioritization of Vulnerabilities: Not every vulnerability carries equal weight in terms of risk. Therefore, it's essential for organizations to prioritize their efforts in addressing these weaknesses. This prioritization should be based on two key factors: the severity of the vulnerability and its potential impact on the business. By categorizing vulnerabilities according to their severity and assessing their potential consequences on the organization, resources can be allocated more effectively. This strategic approach ensures that critical vulnerabilities, which could significantly harm the business if exploited, receive immediate attention and remediation. Conversely, less severe vulnerabilities may be addressed in due course, depending on available resources and the organization's risk tolerance. In this way, prioritizing remediation efforts helps organizations to manage their cybersecurity risks more efficiently and effectively.
Implementation of a Patch Management Process: A well-defined patch management strategy is essential for the timely and effective application of patches. This includes testing patches before deployment to avoid disruptions.
Continuous Monitoring and Incident Response Planning: Ongoing monitoring of systems and networks allows for the detection of suspicious activities that may indicate exploitation of a vulnerability. An incident response plan guarantees the organization's readiness to respond promptly and efficiently to any security breaches.
Training and Awareness: Educating staff about the importance of cybersecurity and their role in maintaining is an important step. Regular training can significantly reduce the risk of security incidents caused by human error.
Challenges in Vulnerability Management
Navigating the complex terrain of vulnerability management presents a myriad of challenges for organizations. Despite deploying their best efforts and resources, they often encounter obstacles that can hinder their ability to effectively identify, assess, and mitigate vulnerabilities. Navigating the dynamic landscape of cyber threats, alongside resource constraints and technological barriers, presents numerous challenges in safeguarding digital assets. Recognizing these hurdles marks the initial phase in crafting cybersecurity strategies that are both resilient and adaptable.
Scale and Complexity of IT Environments: As IT environments grow in complexity, tracking and managing vulnerabilities across a diverse array of assets becomes increasingly difficult. Solution: Automating asset discovery and management can help organizations maintain an up-to-date inventory, ensuring all assets are accounted for and assessed for vulnerabilities. Deploying a centralized vulnerability management platform can streamline operations, offering a holistic perspective of the organization's security stance.
Evolving Threat Landscape: The fast-paced evolution of cyber threats implies that what is considered secure today might not remain secure tomorrow. Solution: Staying ahead requires a proactive approach, incorporating threat intelligence and predictive analytics to anticipate potential vulnerabilities before they are exploited. Regular training for security teams on the latest threat vectors and attack techniques is also vital to remain vigilant against new threats.
Resource Constraints and Prioritization Issues: With limited resources and an overwhelming number of vulnerabilities, organizations struggle to prioritize which vulnerabilities to address first. Solution: Employing a risk-based approach to vulnerability management can help in prioritizing vulnerabilities based on their potential impact and the likelihood of exploitation. Tools that offer risk scoring based on these factors can assist in focusing efforts on the most critical vulnerabilities first.
Integration with Existing Security Processes and Tools: Siloed security tools and processes can hinder the effectiveness of vulnerability management. Solution: Integrating vulnerability management solutions with existing security tools and workflows can enhance visibility and response capabilities. This can be achieved through API integrations and adopting platforms that support interoperability. Establishing cross-functional teams that include IT operations, security, and compliance roles can also foster a more cohesive approach to managing vulnerabilities.

Vulnerability management is a critical component of a comprehensive cybersecurity strategy. By understanding its key components, adhering to best practices, and navigating its challenges, organizations can significantly enhance their security posture. As the digital landscape evolves, so too must vulnerability management strategies. Staying informed about future trends and technological advancements will be necessary for security professionals looking to protect their organizations against emerging threats.

